DEFCON 2025
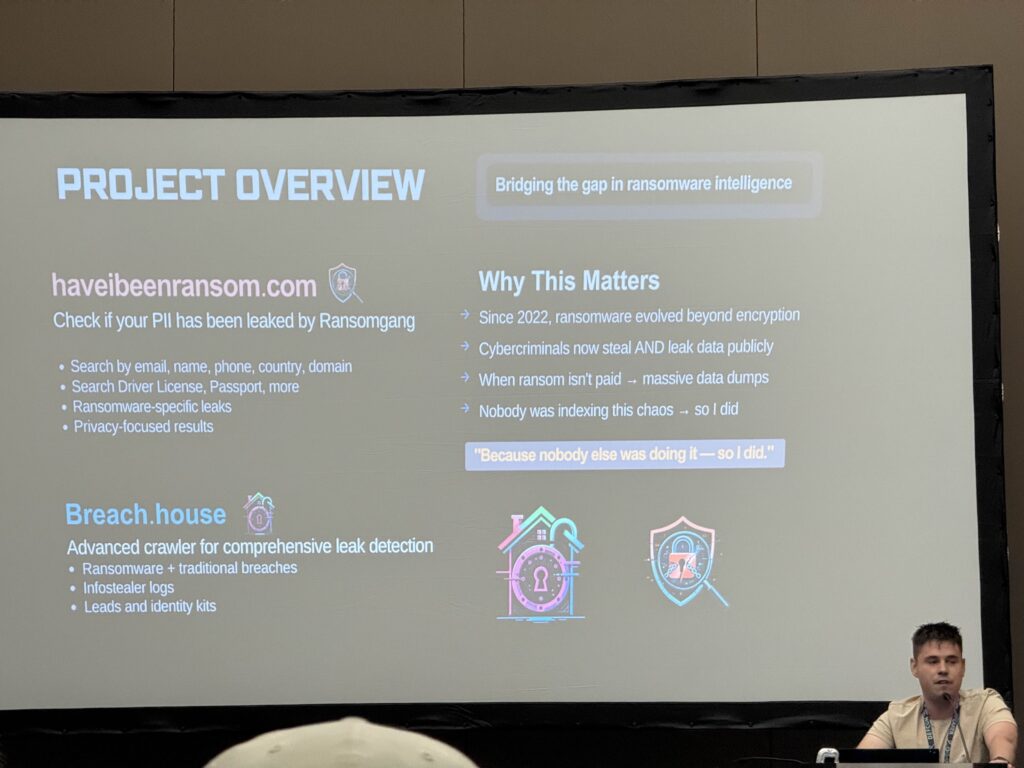
Lessons Learned: DLP solutions can be bypassed with creative encoding and protocol use. Maritime systems are vulnerable due to legacy interfaces. Password managers are susceptible to browser-based attacks. Geopolitical interests drive targeted data breaches, especially in healthcare. Quantum computing poses a real threat to encryption standards and requires proactive planning. Social engineering remains a major threat even in well-trained environments, and OSINT can be weaponized against organizations. Employee vigilance and verification protocols are essential to defend against these tactics. Tools like haveibeenransom offer valuable visibility into ransomware-related PII exposure.
Day 0 (Wednesday): Took an Uber from my apartment to the STL airport, then flew to Vegas, when I landed in Vegas I took an Uber to the hotel, checked-in to the hotel, walked a mile in 110 degree weather to a restaurant named Cleaver to get a steak dinner – unfortunately the AC at my hotel broke and I didn’t get any sleep. I attempted to call the front desk around 10 PM but no one picked up.
Day 0 TLDR: Vegas is expensive and my hotel was very bad.
Day 1 (Thursday): I told the hotel front desk that my AC was broke so they sent someone to fix it that morning, I walked to the convention center, waited in “linecon” for over an hour then got my DEFCON badge, and a free bag with some DEFCON themed stickers. Then I volunteered at Toxic BBQ which is a yearly outdoor BBQ event sponsored by DEFCON, I setup grills outdoor and made burgers at a local park, then took an Uber to a sushi restaurant, then went to a free pool party & networking event hosted by DEFCON. There were over 30,000 attendees at Defcon, it is exceedingly overwhelming.
Day 1 TLDR: Defcon had over 30,000 attendees, lines are multiple hours long, and Uber is expensive.
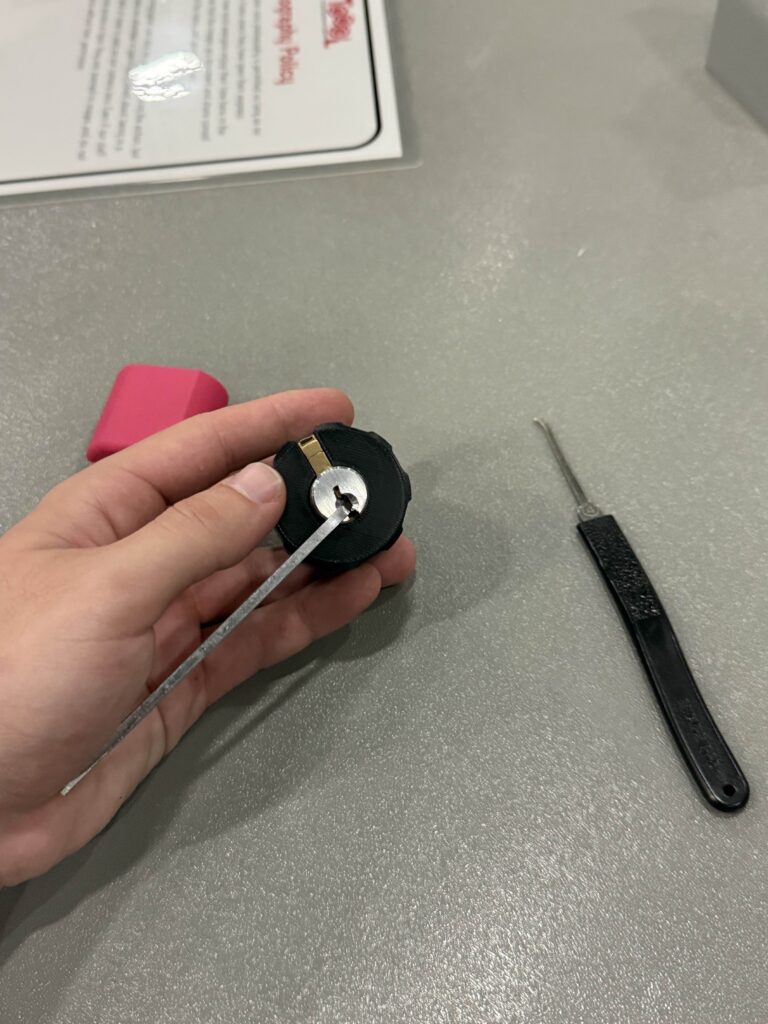
Day 2 (Friday): First official day of Defcon, I ordered a delivery breakfast burrito and coffee for breakfast to my hotel, then walked to the convention center. I went to the social engineering village, participations are given a fortune 500 target company like McDonalds several months before the competition and are tasked with performing as much OSINT as possible and collecting relevant information like shifts, names, phone numbers, badge numbers, anti-virus software used etc. During the event they are put in a sound proof booth and given 22 minutes to collect as much specific information as possible from their victim as possible. One user pretended to be from a nearby McDonalds store calling to ask if they could borrow cheese, the participant recited the specific store number they were calling from, recited their badge number, etc. and probed for specific information like if the intranet website was online and working as intended, and if they were having issues with their email, and asked to confirm which email provider they were using (Outlook, Gmail etc.), then the participant mentioned they’re having issues with their security software and asked the target which anti-virus software is installed on the workstation and if they could confirm which browser they’re using. Another participant prefaced as internal IT and inquired if patching was typically done automatically or if users had to manually update their workstations, some targets pushed back and emphasized that corporate internal IT should know this information or would typically email rather than call a random store associate, and even referenced their recent phishing training which prepared them for such attacks. Next, I visited the physical security village and learned how to use a flipper zero to clone badges to unlock doors and bypass alarms, then I learned how to go under a door to unlock it using a makeshift string and a metal wire by an actual physical penetration tester. I also learned how to open a car door using a tool. Then I went to the lockpicking village to learn how to pick a lock by hand. I went to the car hacking village to learn how a car can be remotely started, controlled, and manipulated. Then I stopped in the aerospace village to learn how drones can be remotely operated or hacked. I got a picture with John Hammond and Network Chuck in the IOT village then went to my first talk about a tool named haveibeenransom which is a tool similar to haveibeenpwned but is designed to check if your PII has been leaked by ransomware, info stealers or traditional breaches. Finally, I took an Uber from the convention center to the hotel, then took another Uber to a Thai restaurant for dinner then took an Uber back to the hotel.
Day 2 TLDR: Social engineering is still a highly effective method of infiltration and recon even in fortune 500 companies with an emphasis on cybersecurity, mandatory cybersecurity awareness training is helpful but many employees are still too trusting, we should encourage employees to challenge callers by asking clarifying questions, these questions can be used to weed out many social engineers. OSINT can be used to gather vast amounts of information like badge numbers, store numbers, titles, corporate emails, organizational structure/s, internal policies, and procedures etc. employees should always be weary of what we put online as this could be used against us. Employees should be trained on how to confirm if someone is legitimately calling from corporate IT to mitigate social engineering attempts (secret code or something that only an employee could know), and they should never answer any questions regarding their organization’s policies, infrastructure, tooling, configurations etc. Lastly, haveibeenransom is a tool developed by a speaker at Defcon which is similar to haveIbeenpwned but is specifically designed to check if your PII has been leaked by a ransomware gang, info stealer or is a part of a traditional breach.
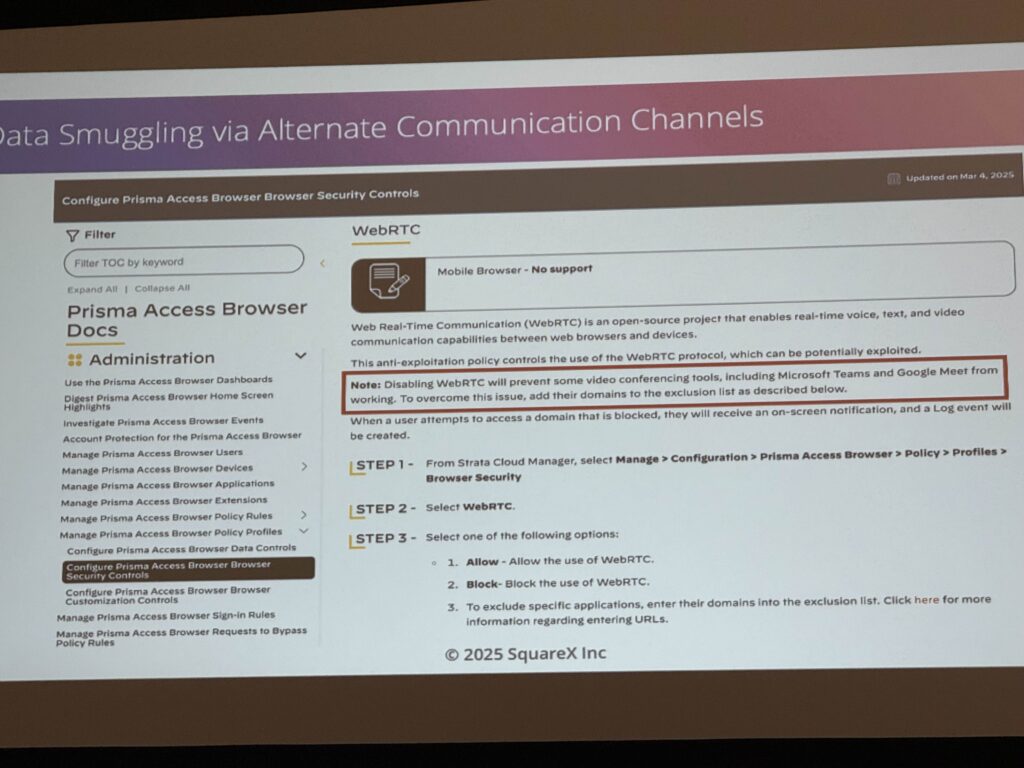
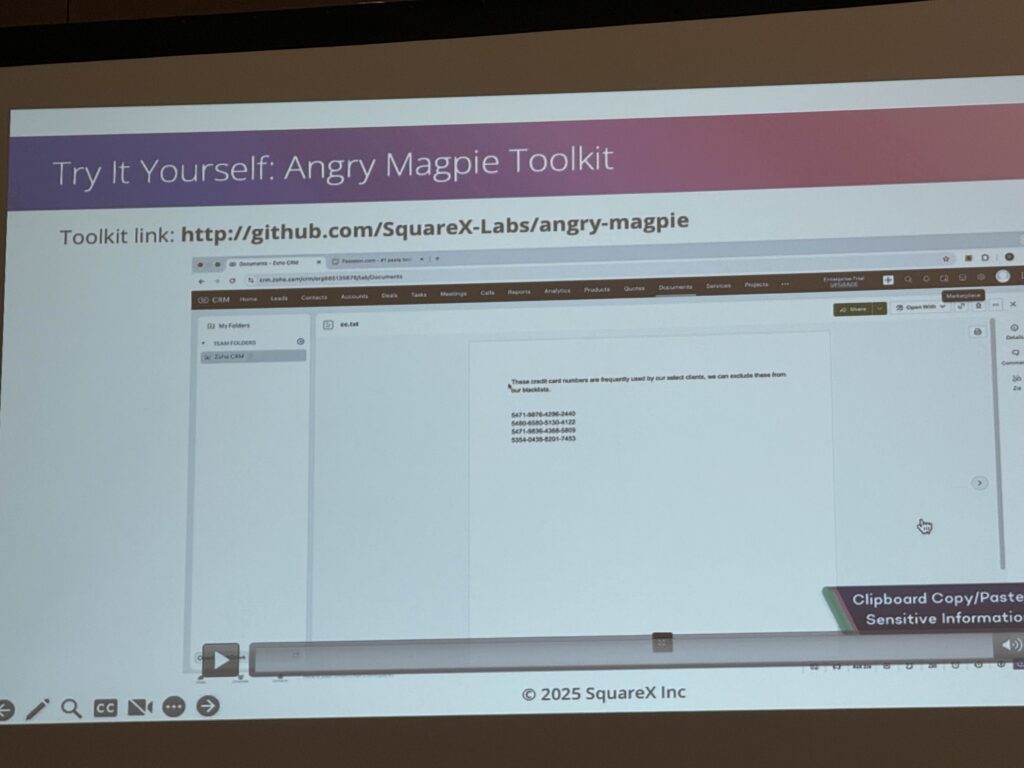
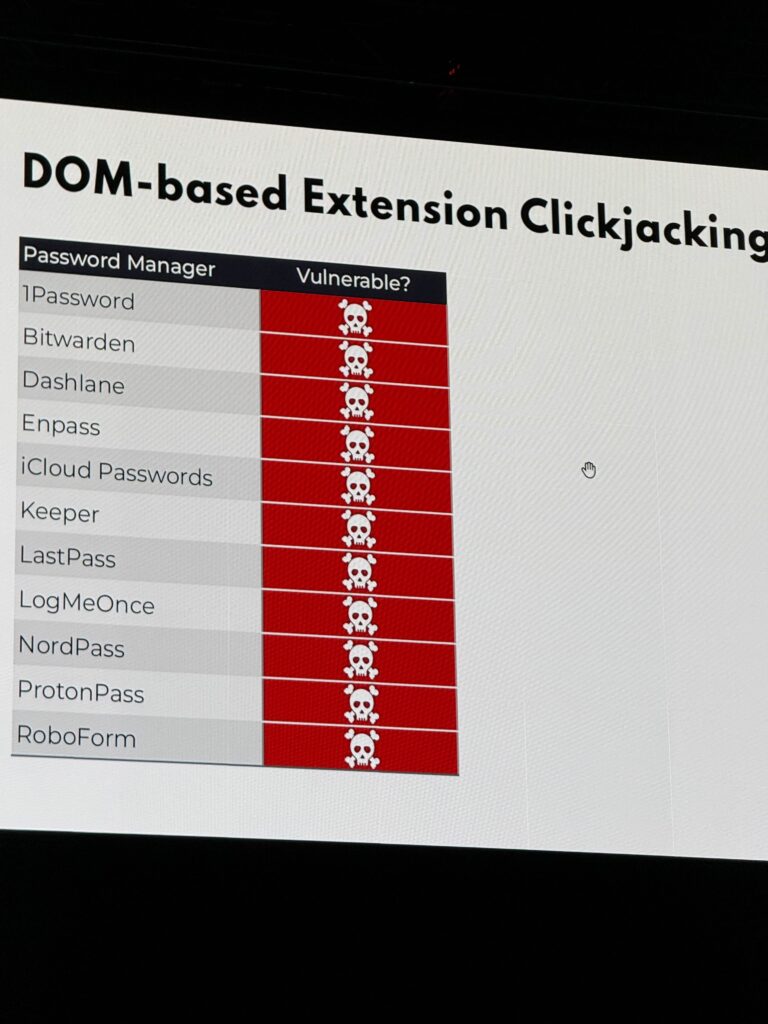
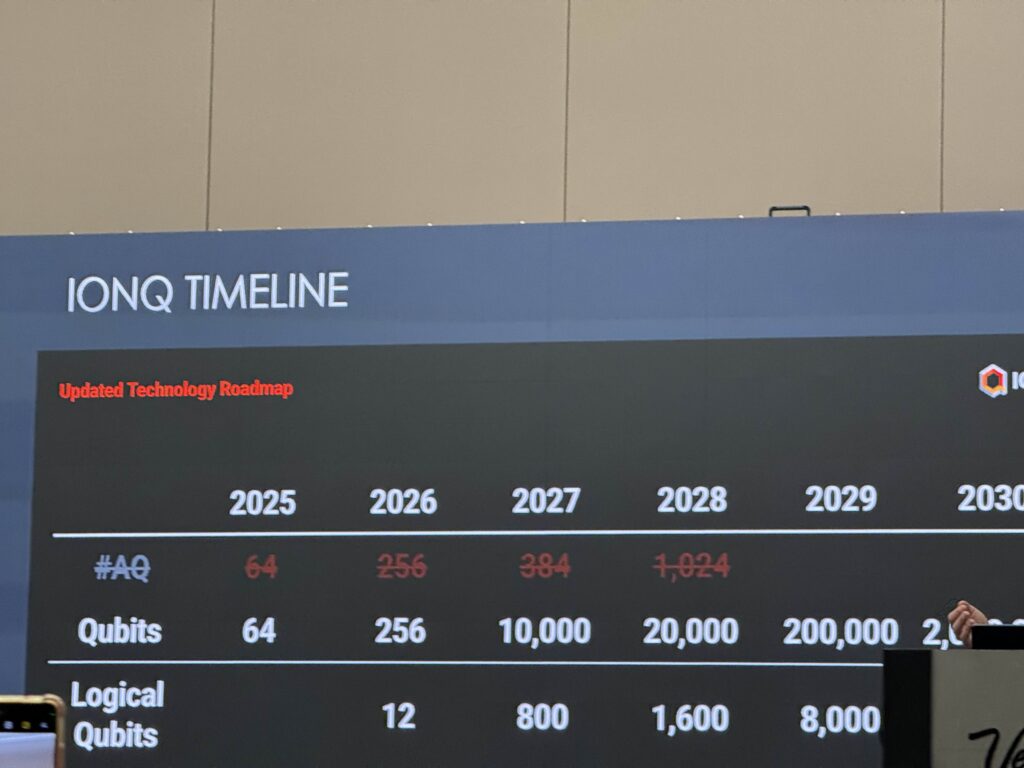
Day 3 (Saturday): I walked to the convention center and attended a talk named “Angry Magpie – DLP Bypass Simulator” which is a browser extension that allows users to bypass enterprise browser and endpoint DLP controls like Netskope, Palo Alto Prisma, Zscaler, G-suite etc. by splicing the data uploaded into chunks and uploading them bits at a time then putting it all together automatically on the server/receiver end (credit + card + number), adding additional characters like a white string to the end of the text to evade detection, and converting sensitive text to base64, then converting it back automatically on the server/receiver end. Certain non-standard protocols like WebRTC can also be used to exfiltrate data as these protocols are not detected by DLP solutions like Netskope. This entire toolkit is available on GitHub. Then I went to the maritime village and learned that boats, even those which are a bit outdated and only have GPS and navigation functionality can be hacked and typically have some sort of input/output for troubleshooting methods, a DEFCON attendee was able to move the boat’s engine from left to right using their computer. Then, I rode with a newfound friend from the convention center to an authentic ramen shop in their rental car, then we went back to the convention center for another talk which was about clickjacking browser extensions to exfiltrate data stored within the password managers like credentials, credit cards, and MFA codes. All major password managers like LastPass, NordPass, ProtonPass etc. are vulnerable to this type of clickjacking attack. Next, I attended a talk about China’s interest in medical record data, this data is used to advance the CCP’s strategic interest in being the world’s supplier of medical raw materials and research, this goal was emphasized after COVID – this type of data has historically been purchased in mass by China but due to emerging regulations in the west it is anticipated that this data will be harvested through other means like hacking, it was anticipated that attacks originating from China to health agencies will likely increase as a result of these regulations and protections. Then I attended a talk about quantum computing, and how it will break encryption by 2030 – the US federal government has advised agencies to prepare and enact a plan by 2035 to mitigate quantum computing however companies like IBM anticipate that encryption may be cracked as late as 2031 and have firm roadmaps, associated with the number of Qubits and logical Qubits required to break encryption. Then, I took an uber from the convention center back to the hotel to decompress, and later walked to a nearby Mexican restaurant where I had dinner and drinks.
Day 3 TLDR:I attended a talk called “Angry Magpie – DLP Bypass Simulator” which showcased a browser extension that can bypass enterprise DLP controls like Netskope, Palo Alto Prisma, Zscaler, and G-suite. It works by slicing sensitive data into chunks, adding benign characters, converting it to base64, and reassembling it on the receiver’s end. It also uses non-standard protocols like WebRTC to evade detection. The toolkit is available on GitHub. Later, I learned that maritime vessels—even older ones with basic GPS and navigation systems—can be hacked. A DEFCON attendee demonstrated control over a boat’s engine using a laptop, exploiting its input/output interfaces. I attended another talk on clickjacking attacks targeting password manager browser extensions. These attacks can exfiltrate sensitive data from password managers like LastPass, NordPass, and ProtonPass, including all credentials in your vault, credit card info, and MFA codes etc. Next I attended a session on China’s interest in biotech highlighted how the CCP uses this data to advance its strategic goals in medical research and raw material supply. Due to increasing Western regulations, China is expected to shift from purchasing this data, to hacking health agencies to obtain this data. Finally, I attended a quantum computing talk that warned encryption could be broken by 2030. The US government advises mitigation plans by 2035, but companies like IBM anticipate breakthroughs as early as 2031, depending on qubit advancements (logical and physical).
Day 4 (Sunday): The last full day of the conference, I walked to the convention center and joined the social engineering village once more, purchased a $30 T-shirt from the village, and watched the awards ceremony which celebrated the best social engineers who participated in the competition, then the village had an event named “Cold Calls” in which random attendees are put in the booth and given a target like a local convenience or shoe store and given 5 minutes on the clock to gather specific information like what type of anti-virus software or browser the target uses, many attendees were unsuccessful given they had no time to prepare for the attack and did not have any OSINT notes as the participants of day #2 did. One attendee was a young girl, who used a pretext of a young college student doing a random study for an assignment in her cybersecurity course and was able to socially engineer a local shoe store into giving her all of the desired information with no questions asked. Lastly, I attended a talk regarding exploiting end-to-end encrypted messengers like Signal, in this talk the speaker demonstrated how you can affectively track a recipients location and routine using their delivery status of a message (If delivered in a certain amount of time, the recipient is using their computer and is home, if it is not delivered and is queued by the server the user is not home) there is a rate limit to signal’s messaging service and this can be used to DOS a recipient and prevent them from receiving or sending messages, while simultaneously knowing which device they are using based on the response time given to the sender from the server, the server will affectively DOS the recipient. Lastly I took an uber back to the hotel, then took another uber to a sushi restaurant for dinner.
Day 4 TLDR: I joined the social engineering village again and watched the awards ceremony recognizing top participants. The village hosted an event called “Cold Calls” where random attendees had five minutes to gather specific technical details from real businesses like antivirus or browser types. Many failed due to lack of preparation, but one young girl succeeded using a college student pretext to extract all required info from a shoe store. I then attended a talk on exploiting end-to-end encrypted messengers like Signal. The speaker showed how message delivery timing can reveal a recipient’s location and device usage. Signal’s rate limits can be abused to DOS a user while also identifying their device based on server response behavior.
Day 5 (Monday): Check out of hotel, uber to airport, fly to STL, uber back to apartment, work for the rest of the afternoon.
Day 5 TLDR: N/A
Summary: I attended a talk called “Angry Magpie – DLP Bypass Simulator” which showcased a browser extension created by a DEFCON speaker that can bypass enterprise DLP controls like Netskope, Palo Alto Prisma, Zscaler, and G-suite. It works by slicing sensitive data into chunks, adding benign characters, converting it to base64, and reassembling it on the receiver’s end. It also uses non-standard protocols like WebRTC to evade detection. The toolkit is available on GitHub. Later, I learned that maritime vessels—even older ones with basic GPS and navigation systems—can be hacked. A DEFCON attendee demonstrated control over a boat’s engine using a laptop, exploiting its input/output interfaces. I attended another talk on clickjacking attacks targeting password manager browser extensions. These attacks can exfiltrate sensitive data from password managers like LastPass, NordPass, and ProtonPass, including all credentials in your vault, credit card info, and MFA codes etc. Next I attended a session on China’s interest in biotech highlighted how the CCP uses this data to advance its strategic goals in medical research and raw material supply. Due to increasing Western regulations, China is expected to shift from purchasing this data, to hacking health agencies to obtain this data. Finally, I attended a quantum computing talk that warned encryption could be broken by 2030. The US government advises mitigation plans by 2035, but companies like IBM anticipate breakthroughs as early as 2031, depending on qubit advancements (logical and physical). I joined the social engineering village again, the village hosted an event called “Cold Calls” where random attendees had five minutes to gather specific technical details from real businesses like antivirus or browser types. Many failed due to lack of preparation, but one young girl succeeded using a college student pretext to extract all required info from a shoe store. Social engineering is still a highly effective method of infiltration and recon even in fortune 500 companies with an emphasis on cybersecurity. Mandatory cybersecurity awareness training is helpful but many employees are still too trusting. We should encourage employees to challenge callers by asking clarifying questions, these questions can be used to weed out many social engineers. OSINT can be used to gather vast amounts of information like badge numbers, store numbers, titles, corporate emails, organizational structures, internal policies, and procedures. Employees should always be weary of what we put online as this could be used against us. Employees should be trained on how to confirm if someone is legitimately calling from corporate IT to mitigate social engineering attempts (secret code or something that only an employee could know), and they should never answer any questions regarding their organization’s policies, infrastructure, tooling, configurations etc. Lastly, haveibeenransom is a tool developed by a speaker at DEFCON which is similar to haveIbeenpwned but is specifically designed to check if your PII has been leaked by a ransomware gang, info stealer or is a part of a traditional breach.